Secure Vectors Accredited as a PCI DSS Approved Scanning Vendor (ASV)
/0 Comments/in Knowledge, Knowledge-home, Knowledge-home, News📢Secure Vectors Accredited as a PCI DSS Approved Scanning Vendor (ASV):
🌏Among the Few Compliance Firms in Asia-Pacific Holding Four PCI Certifications
Secure Vectors Technologies Inc. is now officially recognized by the PCI SSC as a PCI DSS Approved Scanning Vendor (ASV), offering trusted, industry-grade vulnerability scanning services.
Secure Vectors International now holds four globally recognized PCI certifications:
✅PCI DSS QSA(Qualified Security Assessor)
✅PCI 3DS Assessor
✅PCI PIN Security Assessor
✅PCI DSS ASV(Approved Scanning Vendor)
PCI DSS, 3DS, and PIN Security are three of the most critical standards in the payment card industry. With the addition of PCI ASV accreditation—representing advanced technical security expertise—Secure Vectors now offers comprehensive, end-to-end certification services for the financial and payment sectors. Our capabilities span governance, process management, and technical security, delivering a true one-stop PCI compliance solution for our clients.
🔍ASV: The Gold Standard in Vulnerability Scanning and Compliance
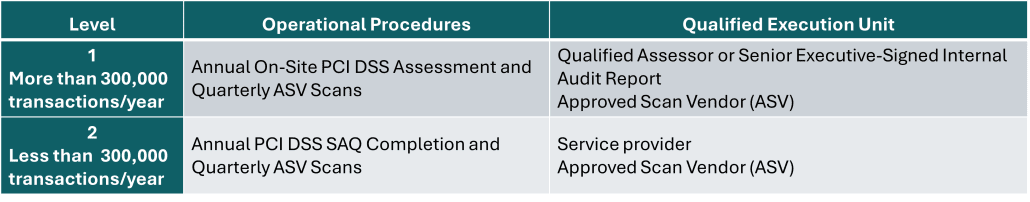
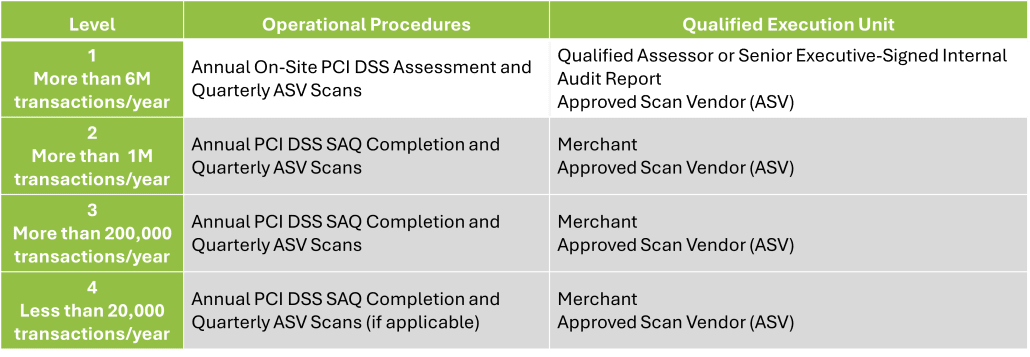
ASV is more than a standard vulnerability scan—it is a comprehensive assessment service validated by the PCI Security Standards Council (PCI SSC). Under PCI DSS requirements, all entities that store, process, or transmit cardholder data must submit quarterly vulnerability scan reports. PCI SSC mandates that all eligible financial and payment organizations use an Approved Scanning Vendor (ASV) to conduct these scans and provide official, validated reports.
Achieving ASV recognition involves three critical requirements:
1️⃣ Scanning Tools – The ASV service’s vulnerability detection methods (including manual procedures, workflows, and technical tools) must thoroughly identify all known vulnerabilities according to PCI SSC standards and complete the full Test Bed scan and analysis within 18 hours.
2️⃣ Execution Team – Engineers and service managers performing the scans must pass PCI SSC professional exams annually, ensuring their knowledge and service processes meet PCI SSC standards.
3️⃣ Reporting Process – Officially audited to ensure accurate interpretation of results, proper handling of false positives, and consistent, traceable reporting formats.
Only after final review and approval by PCI SSC can a company and its scanning solution obtain formal ASV status.
This process tests the ASV provider and solution in:
🔎 Detection Coverage – Ability to cover vulnerabilities across multiple protocol layers
🎯 Assessment Accuracy – Ability to distinguish false positives from real risks
📋 Reporting Rigor – Ability to provide audit-ready compliance evidence
✨ASV: Globally Trusted by the Payment Industry
📅 In October 2025, Secure Vectors Technologies Inc. officially passed the PCI SSC review and was listed as an Approved Scanning Vendor (ASV).
This recognition represents:
Industry Recognition – Only ASV scan reports are accepted as valid evidence for PCI DSS compliance audits in the financial payment sector.
Validated Technology, Team, and Processes – All aspects have been verified by PCI SSC.
Trusted Benchmark in Payments – As one of the few consulting firms in the Asia-Pacific region holding QSA × 3DS × PIN Security × ASV certifications, Secure Vectors International helps enterprises maintain ongoing compliance across multiple regulatory frameworks.
Looking ahead, we aim to use this achievement as a foundation to not only assist financial and payment organizations with ASV scans and compliance reporting but also to provide external domain vulnerability scanning, reporting, and related services across industries and regions — helping enterprises turn compliance into a business growth advantage.
Contact Us Today for Expert ASV Vulnerability Scan Support
👉 Contact Us

FAQ
Q1: What is PCI DSS ASV?
ASV (Approved Scanning Vendor) is an external vulnerability scanning service recognized by the PCI Security Standards Council (PCI SSC), whose scanning solution has been tested and approved. Under PCI DSS Requirement 11.3.2, organizations must have quarterly external scans performed by an ASV and receive passing reports to maintain nearly 12 months of compliance evidence.
Q2: How is ASV different from regular scanning tools?
ASV is more than just a scanning tool — it is a complete scanning solution validated by PCI SSC. Its tools, execution team, procedures, and reporting workflow must all pass official testing and audits. Only PCI-recognized ASV scan reports can serve as formal evidence for PCI DSS compliance audits and are widely trusted in the financial and payment industries.